Bumps [k8s.io/apimachinery](https://github.com/kubernetes/apimachinery) from 0.32.2 to 0.32.3. - [Commits](https://github.com/kubernetes/apimachinery/compare/v0.32.2...v0.32.3) --- updated-dependencies: - dependency-name: k8s.io/apimachinery dependency-type: direct:production update-type: version-update:semver-patch ... Signed-off-by: dependabot[bot] <support@github.com> Co-authored-by: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com> |
||
|---|---|---|
| .github | ||
| cfg | ||
| check | ||
| cmd | ||
| docs | ||
| hack | ||
| helper_scripts | ||
| hooks | ||
| integration/testdata | ||
| internal/findings | ||
| .gitignore | ||
| .golangci.yaml | ||
| .goreleaser.yml | ||
| .yamllint.yaml | ||
| codecov.yml | ||
| CONTRIBUTING.md | ||
| Dockerfile | ||
| Dockerfile.fips.ubi | ||
| Dockerfile.ubi | ||
| entrypoint.sh | ||
| fipsonly.go | ||
| go.mod | ||
| go.sum | ||
| job-ack.yaml | ||
| job-aks.yaml | ||
| job-eks-asff.yaml | ||
| job-eks-stig.yaml | ||
| job-eks.yaml | ||
| job-gke.yaml | ||
| job-iks.yaml | ||
| job-master.yaml | ||
| job-node.yaml | ||
| job-tkgi.yaml | ||
| job.yaml | ||
| LICENSE | ||
| main.go | ||
| makefile | ||
| mkdocs.yml | ||
| NOTICE | ||
| OWNERS | ||
| README.md | ||

kube-bench is a tool that checks whether Kubernetes is deployed securely by running the checks documented in the CIS Kubernetes Benchmark.
Tests are configured with YAML files, making this tool easy to update as test specifications evolve.
CIS Scanning as part of Trivy and the Trivy Operator
Trivy, the all in one cloud native security scanner, can be deployed as a Kubernetes Operator inside a cluster. Both, the Trivy CLI, and the Trivy Operator support CIS Kubernetes Benchmark scanning among several other features.
Quick start
There are multiple ways to run kube-bench. You can run kube-bench inside a pod, but it will need access to the host's PID namespace in order to check the running processes, as well as access to some directories on the host where config files and other files are stored.
The supplied job.yaml file can be applied to run the tests as a job. For example:
$ kubectl apply -f job.yaml
job.batch/kube-bench created
$ kubectl get pods
NAME READY STATUS RESTARTS AGE
kube-bench-j76s9 0/1 ContainerCreating 0 3s
# Wait for a few seconds for the job to complete
$ kubectl get pods
NAME READY STATUS RESTARTS AGE
kube-bench-j76s9 0/1 Completed 0 11s
# The results are held in the pod's logs
kubectl logs kube-bench-j76s9
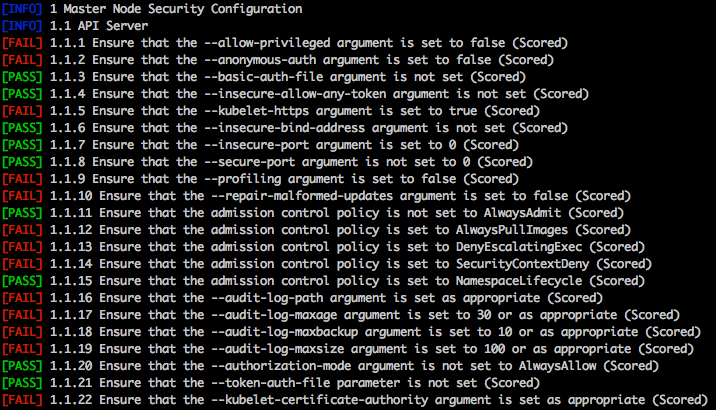
[INFO] 1 Master Node Security Configuration
[INFO] 1.1 API Server
...
For more information and different ways to run kube-bench see documentation
Please Note
-
kube-bench implements the CIS Kubernetes Benchmark as closely as possible. Please raise issues here if kube-bench is not correctly implementing the test as described in the Benchmark. To report issues in the Benchmark itself (for example, tests that you believe are inappropriate), please join the CIS community.
-
There is not a one-to-one mapping between releases of Kubernetes and releases of the CIS benchmark. See CIS Kubernetes Benchmark support to see which releases of Kubernetes are covered by different releases of the benchmark.
By default, kube-bench will determine the test set to run based on the Kubernetes version running on the machine.
- see the following documentation on Running kube-bench for more details.
Contributing
Kindly read Contributing before contributing. We welcome PRs and issue reports.
Roadmap
Going forward we plan to release updates to kube-bench to add support for new releases of the CIS Benchmark. Note that these are not released as frequently as Kubernetes releases.